by Nicole Powers
These days, it’s kinda like your computer illiterate granddad is laying down the law on the internet. Only worse. Cause your computer illiterate granddad doesn’t have the power to send your ass to jail for longer than most rapists for the crime of clicking on the wrong http link. Which is something the US government is trying to do. Fo’ realz. Yep. That.
Case in point. Andrew Alan Escher Auernheimer, a.k.a. @rabite, a.k.a. Weev. He’s just been found guilty on one count of not actually hacking anything and one count of having a list of email addresses, even though no one bothered to prove he ever actually had ’em, tho everyone agrees his mate did. Confusing right? You can totally imagine Gramps throwing his hands in the air at this point and saying to hell with this good-for-nothing with two too many silly-ass names – which is pretty much what the US government is doing.
Part of the problem is that the laws Andrew Alan Escher Auernheimer, fuck it, let’s just call him Weev, has been found guilty of violating – which came into being under the 1986 Computer Fraud and Abuse Act (CFAA) – predate Hypertext Transfer Protocol, the first documented version of which, V0.9, was codified in 1991. In light of the fact that we’ve yet to come up with a fully functioning flux capacitor, as you can imagine, the application of the CFAA on today’s internet works about as well as Doc Brown’s DeLorean time machine.
***
“Couldn’t it be argued that Weev actually did something good and beneficial for society?”
Wait? Wut? If that’s the case, remind me why Grampa Government is trying to throw his ass in jail?
I’m chatting with Jay Leiderman, a chap who knows a thing or three about the law and the internet. He’s an elite California State Bar Certified Criminal Law Specialist-grade lawyer who’s defended several high profile hacktivist types, including Raynaldo Rivera of LulzSec and Commander X of the Peoples Liberation Front. He also happens to be a Twitter ninja, which is how I got to know him. A quick perusal of his @LeidermanDevine twitter feed will tell you Jay’s a rare legit legal animal who clearly gets today’s wobbly whirly web, which is why I called him up to discuss Weev’s wobbly whirly situation, which is as follows…
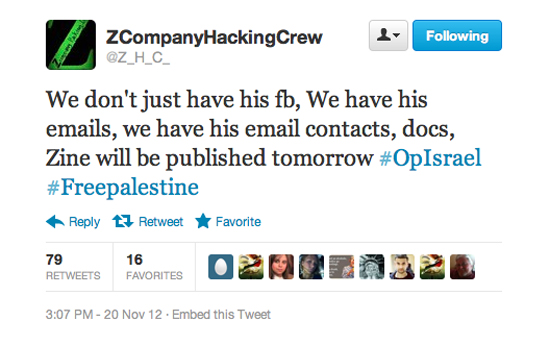
On November 20, 2012, in a Newark, NJ court, Weev was convicted of USC 1028, “identity theft” (as in “stealing” a list of email addresses) and USC 1030 “conspiracy to access a computer device without authorization” –– which, according to Jay, is something we technically all do multiple times every day. Given that Weev was singled out of the entirety of America’s online population for prosecution, in real terms, it’s safe to say what he’s actually more guilty of is embarrassing the fuck out of a Fortune 500 company…and the government no likey that.
Let me explain: Back in 2010 when the iPad first came out, Weev’s mate figured out that AT&T was doing a sloppy ass job with autofill on an app, and in the course of achieving this great technological feat had publicly published the e-mail addresses and ICC-IDs (the identifiers that match a person to their SIM card in a mobile device) of its entire iPad customer base on the web – with no password, no firewall, no fuck off or die warning, no nothing to protect them. Yep. Really. They were that dumb.
“There’s an AT&T web app that had a URL on it with a number at the end, and if you added one to the number you would see the next email address,” explains Weev by phone after I tracked his ass down via teh twitters. Obviously there’s quicker ways to get kicks online than adding a digit to a URL and hitting return (have you tried Googling Goatse?), so Weeve’s ever resourceful mate, Daniel Spitler, created an app called the “iPad 3G Account Slurper” which sucked up well over 100,000 addresses. “My friend just wrote a script to irate though and add one to the number again and again and again,” Weeve tells me. “It’s not fucking rocket science. It’s basic arithmetic. It could have been done manually on any iPad.”
So that explains how they “stole” the list of publicly published email addresses, but why might be a better question to ask. “Comment and criticism against large companies which go unchecked in our country,” replies Weev, when I ask him. “And making a public spectacle and ridiculing them, which I think frankly makes me the best fucking American in the room. We used to be a country that valued criticism of the powerful, and we haven’t really been in the past three decades.”
To add context, at the time, Weev and his mate (who copped a plea bargain) were working under the banner of Goatse Security, and as such, their mission in life was to explore gaping holes (I told you to Google Goatse!). AT&T’s might not have been the sexiest of holes, but it was gaping and it could be argued that it was in the public interest that Goatse Security rummage around in it.
Among the private email addresses that AT&T were publicly publishing were ones belonging to politicians (New York Mayor Michael Bloomberg and White House Chief of Staff Rahm Emanuel), members of the military and multiple government agencies (DARPA, DHS, NSA, FAA and FCC), and high profile media types (Diane Sawyer and New York Times CEO Janet Robinson). Goatse Security could have had much lulz with the list and/or sold it for mucho dinero, an option which the duo allegedly discussed in IRC chats but put aside. Instead, they decided to go to the press to speak truth to power, which was really when the trouble began.
Weev served as Goatse’s spokesperson and spin master. It was his job to liaise with the media and present stories in a way that might titillate us lazy-ass scribes. “Hey, look, I just found a list of email addresses on a bunch publicly accessible web pages” might have been accurate, but it wasn’t the kind of story that would make copy even on the slowest of news days, so Weev sexed it up a bit. In a press release sent to several news outlets he wrote, “I stole your email,” and, like a magician offering to explain a trick, followed it up with, “Let me explain the method of theft.”
Because of this hyperbole, Weev essentially convicted himself on the first count of “identity theft.” The prosecution spent much of their time with Weeve on the stand discussing his use of the words “stole” and “theft” during cross-examination. I mean, I know it’s said that sarcasm is the lowest form of humor, but I didn’t know it was illegal! And speaking of the law’s humor bind spot, the prosecution also referred to Weev’s Encyclopedia Dramatica entry and used that against him, which, given the spoof nature of the site, is tantamount to using a Saturday Night Live skit as legitimate and damning character evidence. I. Kid. You. Not.
At no time did Goatse ever make the list publicly available – AT&T were the only ones doing that. The prosecution never really attempted to prove that Weev possessed the full list of email addresses. What neither side disputes is that Weev tapped the list for a handful of press email contacts (something he would have likely got by calling the media outlets direct anyways), then merely passed on a link to it to a journalist for verification. The journalist in question was Ryan Tate of Gawker. His story ran on June 9th, 2010, and it was because of this that the shit hit the proverbial fan.
“This access would have gone unnoticed if I hadn’t gone to the press. If I hadn’t informed AT&T’s customers,” says Weev. “They’re not really pissed about the access, they’re pissed about the speech attached to the access. God forbid corporations be subject to fair comment and criticism.”
Talking of access, the second count Weev was convicted of – “conspiracy to access a computer device without authorization” – is something that should be cause for concern for anyone that has ever clicked on anything on the web. The way this law – which predates all of One Direction and the hyperlinked internet as we know it – is interpreted means that accessing a “protected computer” could get your ass slung in jail. But what is a “protected computer” and how the fuck are you supposed to know when you’re accessing one? This is where the law gets interesting. And by interesting, I mean really fucking stupid.
“The definition of protected computer comes from comes from the Computer Fraud and Abuse Act of 1986, and in 1986 http hadn’t been invented yet,” says Weev. “This was a long time ago when servers were things that were only accessible by dial-up that every single one universally had a password for. There wasn’t the concept of a public network. At the time, if you were accessing a remote server, and you didn’t have permission to be there it’s clear that it wasn’t public data. But now it’s the age of the internet. We click links every day. You’ve never gotten Google’s permission to go to Google, you’ve never gotten any website’s permission that you’ve visited. It’s the universally understood aspect of the web that you can visit a public http server without pre-written authorization. It’s a ridiculous notion that you need it. And the prosecutor is using an ancient antiquated definition of a protected system, which is any system that engages in interstate commerce. So essentially, every cell phone, every computer, every public web server is a protected system, and the minute you do something that a website operator doesn’t like – if they’re rich enough of course, if they’re a Fortune 500 company – then they can have you.”
That might sound rather dramatic, but Jay, my favorite SG-lovin’ lawyer agrees. “Based upon this case, the government’s new position is that you are required to be clairvoyant in terms of determining what a protected computer is and what a non protected one is,” he tells me. “From now on you have to be a psychic…because if it isn’t password protected but it’s a ‘protected computer’ you’re potentially going to be found guilty like Weev was.”
Thank god there’s free tittysprinkles on the internet, because otherwise the risks of clicking on something you shouldn’t wouldn’t be worth price. As Weev puts it, “The law says every time that you click a link, if the person at the other end has enough money and connections, and they just don’t like you, they can have you arbitrarily thrown in jail by declaring your access – after the fact – unauthorized.”
But how did we get from “something good and beneficial for society” to “free tittysprinkles”? Well, some might see a very obvious linear connection, but those that don’t should consider this; There’s a cat and mouse game that goes on between big business and the internet security community, but it’s a symbiotic relationship nevertheless. And as consumers who are clueless when it comes to code, we should be grateful to those that are scanning for flaws, and pressuring big corporations to sort their shit out on our behalf.
“Perhaps the greatest lesson of Weev’s case is that not only is there no reward for helping these companies patch their holes and fix themselves, indeed now you’re going to be facing ten or fifteen years of prison if you do,” says Jay. “What’s the incentive to make these companies more secure? I mean, you’re better off just hacking them now. You’re better off just hacking these companies and not telling them. If you get caught essentially you’re facing about the same punishment anyway so what’s the difference?”
***
Weev is currently in the process of appealing his conviction. You can donate to help with his legal costs here.
And tell Grampa Government to get off our lawn and out of our emails.
Isn’t it time we upgraded our legal operating system?